Introduction
In the ever-evolving landscape of artificial intelligence (AI), Deepseek AI has emerged as a trailblazer, pushing the boundaries of machine learning, natural language processing (NLP), and deep learning. With its cutting-edge research, state-of-the-art AI models, and innovative applications, Deepseek AI is reshaping industries and redefining the future of technology.
What is Deepseek AI?
Deepseek AI is an advanced AI research organization and technology company dedicated to developing intelligent systems that enhance human capabilities. It focuses on large-scale AI models, including natural language processing (NLP), computer vision, and reinforcement learning, to drive innovation across various domains.
DeepSeek is an AI development firm based in Hangzhou, China. The company was founded by Liang Wenfeng, a graduate of Zhejiang University, in May 2023. Wenfeng also co-founded High-Flyer, a China-based quantitative hedge fund that owns DeepSeek.
Currently, DeepSeek operates as an independent AI research lab under the umbrella of High-Flyer. The full amount of funding and the valuation of DeepSeek have not been publicly disclosed.
DeepSeek focuses on developing open source LLMs. The company’s first model was released in November 2023. The company has iterated multiple times on its core LLM and has built out several different variations. However, it wasn’t until January 2025 after the release of its R1 reasoning model that the company became globally famous.
OpenAI vs. DeepSeek
DeepSeek represents the latest challenge to OpenAI, which established itself as an industry leader with the debut of ChatGPT in 2022. OpenAI has helped push the generative AI industry forward with its GPT family of models, as well as its o1 class of reasoning models.
While the two companies are both developing generative AI LLMs, they have different approaches.

Training innovations in DeepSeek
DeepSeek uses a different approach to train its R1 models than what is used by OpenAI. The training involved less time, fewer AI accelerators and less cost to develop. DeepSeek’s aim is to achieve artificial general intelligence, and the company’s advancements in reasoning capabilities represent significant progress in AI development.
In a research paper, DeepSeek outlines the multiple innovations it developed as part of the R1 model, including the following:
- Reinforcement learning. DeepSeek used a large-scale reinforcement learning approach focused on reasoning tasks.
- Reward engineering. Researchers developed a rule-based reward system for the model that outperforms neural reward models that are more commonly used. Reward engineering is the process of designing the incentive system that guides an AI model’s learning during training.
- Distillation. Using efficient knowledge transfer techniques, DeepSeek researchers successfully compressed capabilities into models as small as 1.5 billion parameters.
- Emergent behavior network. DeepSeek’s emergent behavior innovation is the discovery that complex reasoning patterns can develop naturally through reinforcement learning without explicitly programming them.
DeepSeek large language models
Since the company was created in 2023, DeepSeek has released a series of generative AI models. With each new generation, the company has worked to advance both the capabilities and performance of its models:
- DeepSeek Coder. Released in November 2023, this is the company’s first open source model designed specifically for coding-related tasks.
- DeepSeek LLM. Released in December 2023, this is the first version of the company’s general-purpose model.
- DeepSeek-V2. Released in May 2024, this is the second version of the company’s LLM, focusing on strong performance and lower training costs.
- DeepSeek-Coder-V2. Released in July 2024, this is a 236 billion-parameter model offering a context window of 128,000 tokens, designed for complex coding challenges.
- DeepSeek-V3. Released in December 2024, DeepSeek-V3 uses a mixture-of-experts architecture, capable of handling a range of tasks. The model has 671 billion parameters with a context length of 128,000.
- DeepSeek-R1. Released in January 2025, this model is based on DeepSeek-V3 and is focused on advanced reasoning tasks directly competing with OpenAI’s o1 model in performance, while maintaining a significantly lower cost structure. Like DeepSeek-V3, the model has 671 billion parameters with a context length of 128,000.
- Janus-Pro-7B. Released in January 2025, Janus-Pro-7B is a vision model that can understand and generate images.

Key Features of DeepSeek AI
1. Advanced Deep Learning Models
DeepSeek AI utilizes deep neural networks to analyze and interpret complex datasets. These models are trained on massive amounts of data, enabling them to recognize patterns, make predictions, and improve over time.
2. Natural Language Processing (NLP)
The platform excels in understanding and generating human language. It can perform tasks such as sentiment analysis, language translation, text summarization, and conversational AI, making it a powerful tool for industries like customer service, healthcare, and finance.
3. Computer Vision
DeepSeek AI’s computer vision capabilities allow it to analyze and interpret visual data, such as images and videos. This is particularly useful for applications like facial recognition, object detection, and autonomous vehicles.
4. Reinforcement Learning
The platform employs reinforcement learning to create systems that can learn and adapt through trial and error. This is especially valuable for robotics, gaming, and optimization problems.
5. Scalability and Flexibility
DeepSeek AI is designed to scale seamlessly, making it suitable for both small businesses and large enterprises. Its modular architecture allows users to customize solutions based on their specific needs.
Applications of DeepSeek AI
1. Healthcare
DeepSeek AI is revolutionizing healthcare by enabling early disease detection, personalized treatment plans, and efficient patient management. Its NLP capabilities are used to analyze medical records, while computer vision assists in diagnosing conditions from medical imaging.
2. Finance
In the financial sector, DeepSeek AI is used for fraud detection, risk assessment, and algorithmic trading. Its ability to process large datasets in real-time makes it an invaluable tool for financial institutions.
3. Retail
Retailers use DeepSeek AI to enhance customer experiences through personalized recommendations, inventory management, and demand forecasting. Its computer vision capabilities also enable cashier-less stores and automated checkout systems.
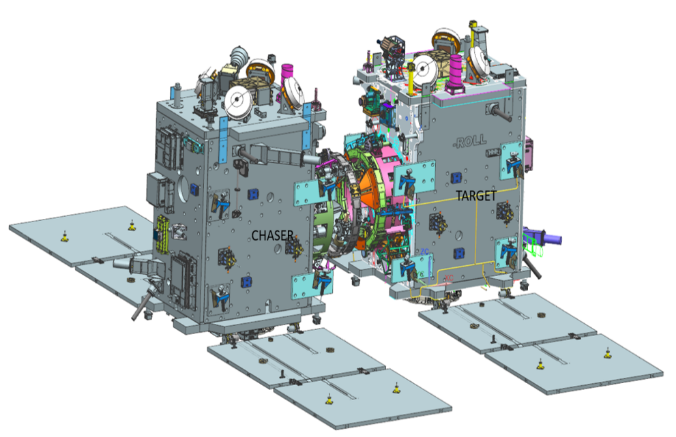
4. Autonomous Vehicles
DeepSeek AI plays a crucial role in the development of self-driving cars. Its computer vision and reinforcement learning algorithms enable vehicles to navigate complex environments safely and efficiently.
5. Customer Service
The platform’s NLP capabilities power intelligent chatbots and virtual assistants, improving customer interactions and reducing response times.

Advantages of DeepSeek AI
1. High Accuracy
DeepSeek AI’s advanced algorithms deliver highly accurate results, minimizing errors and improving decision-making.
2. Real-Time Processing
The platform can process data in real-time, making it ideal for applications that require immediate insights, such as fraud detection and autonomous driving.
3. Cost-Effective
By automating repetitive tasks and optimizing processes, DeepSeek AI helps businesses reduce operational costs.
4. Continuous Learning
DeepSeek AI’s models are designed to learn and adapt over time, ensuring that they remain relevant and effective as new data becomes available.
Challenges and Limitations
While DeepSeek AI offers numerous benefits, it also faces certain challenges:
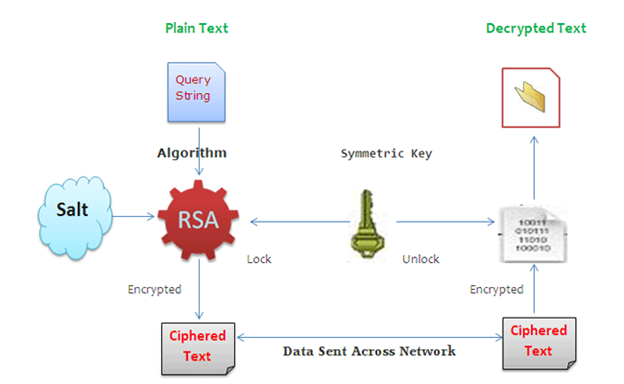
1. Data Privacy
The platform relies on large datasets, raising concerns about data privacy and security. Ensuring compliance with regulations like GDPR is essential.
2. Bias in AI Models
Like all AI systems, DeepSeek AI is susceptible to biases present in the training data. Addressing this issue requires careful data curation and model validation.
3. High Computational Requirements
DeepSeek AI’s advanced algorithms require significant computational resources, which can be a barrier for smaller organizations.
The Future of DeepSeek AI
DeepSeek AI is poised to play a pivotal role in shaping the future of AI. Here are some potential developments:
1. Integration with IoT
DeepSeek AI could be integrated with the Internet of Things (IoT) to create smarter, more connected environments. For example, it could enable intelligent home automation systems or optimize industrial processes.
2. Enhanced Human-AI Collaboration
Future iterations of DeepSeek AI may focus on improving human-AI collaboration, making it easier for non-experts to leverage AI capabilities.
3. Ethical AI Development
As AI becomes more pervasive, ensuring ethical development and deployment will be critical. DeepSeek AI is likely to incorporate features that promote transparency, fairness, and accountability.
4. Expansion into New Industries
DeepSeek AI has the potential to expand into new industries, such as agriculture, education, and entertainment, driving innovation and creating new opportunities.
Conclusion
DeepSeek AI represents a significant leap forward in the field of artificial intelligence. Its advanced capabilities, coupled with its versatility and scalability, make it a powerful tool for solving complex problems across industries. While challenges remain, the platform’s potential to transform the way we live and work is undeniable. As AI continues to evolve, DeepSeek AI is well-positioned to lead the charge, paving the way for a smarter, more connected future.
References
- DeepSeek AI Official Website https://www.deepseek.ai The official website provides detailed information about the platform’s features, applications, and case studies.
- Deep Learning for AI by Yoshua Bengio, Yann LeCun, and Geoffrey Hinton https://www.nature.com/articles/s42256-019-0055-0 This article explores the fundamentals of deep learning and its role in advancing AI.
- Natural Language Processing: A Comprehensive Guide by Jacob Devlin https://towardsdatascience.com/nlp-a-comprehensive-guide-825b1b8a1f2c A detailed guide to natural language processing and its applications.
- Computer Vision: Algorithms and Applications by Richard Szeliski https://szeliski.org/Book/ This book provides an in-depth look at computer vision techniques and their real-world applications.
- Reinforcement Learning: An Introduction by Richard S. Sutton and Andrew G. Barto https://mitpress.mit.edu/books/reinforcement-learning-second-edition A foundational text on reinforcement learning and its applications.
- Ethical AI: Challenges and Solutions by Timnit Gebru https://arxiv.org/abs/2005.14165 This paper discusses the ethical challenges of AI and potential solutions.
By understanding and leveraging the capabilities of DeepSeek AI, businesses and individuals can unlock new possibilities and drive innovation in their respective fields. As AI continues to evolve, platforms like DeepSeek AI will undoubtedly play a central role in shaping the future.